 Kali Linux can be used for many things, but it
probably is best known for its ability to penetration test, or “hack,” WPA and
WPA2 networks. There are hundreds of Windows applications that claim they can
hack WPA; don’t get them! They’re just scams, used by professional hackers, to
lure newbie or wannabe hackers into getting hacked themselves.
Kali Linux can be used for many things, but it
probably is best known for its ability to penetration test, or “hack,” WPA and
WPA2 networks. There are hundreds of Windows applications that claim they can
hack WPA; don’t get them! They’re just scams, used by professional hackers, to
lure newbie or wannabe hackers into getting hacked themselves. Wi-Fi Protected Access (WPA) and Wi-Fi Protected Access II (WPA2) are two
security protocols and security certification programs developed by the Wi-Fi
Alliance to secure wireless computer networks. The Alliance defined these in
response to serious weaknesses researchers had found in the previous system,
WEP (Wired Equivalent Privacy)
Wi-Fi Protected Access (WPA) and Wi-Fi Protected Access II (WPA2) are two
security protocols and security certification programs developed by the Wi-Fi
Alliance to secure wireless computer networks. The Alliance defined these in
response to serious weaknesses researchers had found in the previous system,
WEP (Wired Equivalent Privacy)A flaw in a feature added to Wi-Fi, called Wi-Fi Protected Setup (WPS), allows WPA and WPA2 security to be bypassed and effectively broken in many situations. Many access point they have a Wifi Protected Setup enabled by default (even after we hard reset the access point).
These are things that you’ll need:
A successful install of Kali Linux.
A wireless adapter capable of injection/monitor mode. Some computers have network cards capable of this from the factory.
A wordlist to attempt to “crack” the password once it has been captured
Time and patients
NOTE: It is only for educational purpose and perform all the steps at your own risk I am not responsible for any damage done to your device during the entire process .If you find any difficulty in the process than feel free to comment bellow.
Now
follow the steps to get into someone’s WIFI network , Lets get started:
1.
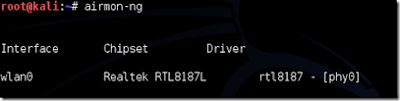
Disconnect from all wireless networks, open a Terminal,
and type airmon-ng .
wlan0.
This will list all of the wireless cards
that support monitor (not injection) mode. If no cards are listed, try
disconnecting and reconnecting the adapter (if you’re using one) and check that
it supports monitor mode. If you’re not using an external adapter, and you
still don’t see anything listed, then your card doesn’t support monitor mode,
and you’ll have to purchase an external one (see the link in the requirements).
You can see here that my card supports monitor mode and that it’s listed as
2.
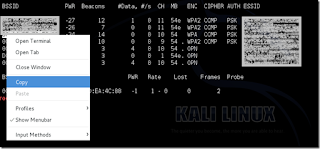
Type airodump-ng followed by
the name of the new monitor interface, which is probably mon0.
3.
Type airodump-ng followed by the name
of the new monitor interface, which is probably mon0.
Airodump
will now list all of the wireless networks in your area, and a lot of useful
information about them. Locate your network or the network that you have
permission to penetration test. Once you’ve spotted your network on the ever-populating
list, hit Ctrl + C on your keyboard to stop the process. Note
the channel of your target network.
4.
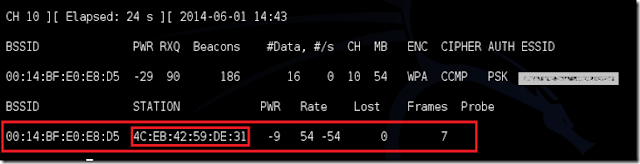
Now type this command: airodump-ng
-c [channel] --bssid [bssid] -w /root/Desktop/ [monitor interface] Replace
[channel] with the channel of your target network. Paste the network BSSID
where [bssid] is, and replace [monitor interface] with the name of your monitor-enabled
interface, (mon0).A complete command should look like this: airodump-ng -c 10 --bssid 00:14:BF:E0:E8:D5 -w
/root/Desktop/ mon0.
5.
Airodump with now monitor only the target
network, allowing us to capture more specific information about it. What we’re
really doing now is waiting for a device to connect or reconnect to the
network, forcing the router to send out the four-way handshake that we need to
capture in order to crack the password.
Also, four files should show up on your desktop, this is where the handshake
will be saved when captured, so don’t delete them! But we’re not really going
to wait for a device to connect, no, that’s not what impatient hackers do.
We’re actually going to use another cool-tool that belongs to the aircrack
suite called aireplay-ng, to speed up the process. Instead of waiting for a
device to connect, hackers can use this tool to force a device to reconnect by
sending deauthentication (deauth) packets to one of the networks devices,
making it think that it has to reconnect with the network.Of course, in order
for this tool to work, there has to be someone else connected to the network
first, so watch the airodump-ng and wait for a client to show up. It might take
a long time, or it might only take a second before the first one shows. If none
show up after a lengthy wait, then the network might be empty right now, or
you’re to far away from the network.
You can see in this picture, that a client has appeared on our network, allowing us to start the next step.
You can see in this picture, that a client has appeared on our network, allowing us to start the next step.
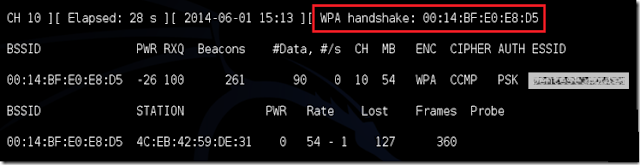
6.
Leave airodump-ng running and open a
second terminal. In this terminal, type this command:
aireplay-ng –0 2 –a [router bssid] –c [client bssid] mon0
My complete command looks like this:
aireplay-ng –0 2 –a 00:14:BF:E0:E8:D5 –c 4C:EB:42:59:DE:31 mon0
My complete command looks like this:
aireplay-ng –0 2 –a 00:14:BF:E0:E8:D5 –c 4C:EB:42:59:DE:31 mon0
7.
Upon hitting Enter, you’ll see aireplay-ng send the
packets. If you were close enough to the target client, and the
deauthentication process works, this message will appear on the airodump screen
(which you left open):
This means that the handshake has been captured, the password is in the
hacker’s hands, in some form or another. You can close the aireplay-ng terminal
and hit Ctrl + C on the airodump-ng terminal to stop
monitoring the network, but don’t close it yet just incase you need some of the
information later.
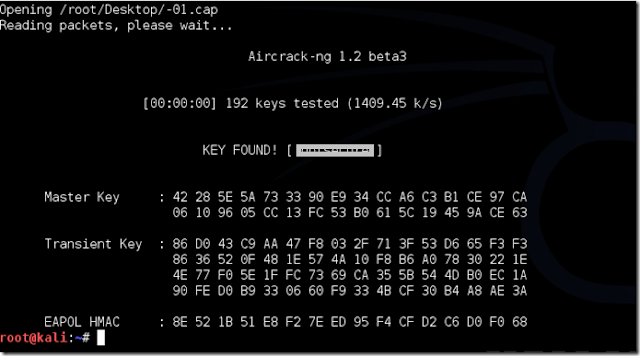
8. This
concludes the external part of this tutorial. From now on, the process is
entirely between your computer, and those four files on your Desktop. Actually,
it’s the .cap one, that is important. Open a new Terminal, and type in this
command:
aircrack-ng -a2 -b [router bssid] -w [path to wordlist]
/root/Desktop/*.cap
9.
Aircrack-ng will now launch into the process of
cracking the password. However, it will only crack it if the password happens
to be in the wordlist that you’ve selected. Sometimes, it’s not. If this is the
case, you can try other wordlists






0 comments:
Post a Comment